
Remember your first username? If you were anything like me in the early 2000s—too young to surf the web but excited about the possibilities of connecting with the rest of the world—your username probably makes you cringe today.
Self-expression is the main driver for my internet usage. Over the years, I've created various usernames representing different parts of me at distinct periods of my life. From Millsberry to Myspace, each new website meant a new profile, leading to a fragmented experience. The most annoying part is that there's no connection between my profiles or "identities", so I have to remember all my passwords or rely on a password manager. Unfortunately, password managers are susceptible to security breaches.
This fragmentation of identity on the web poses a significant challenge: How do we manage these scattered identities efficiently and securely?
Many organizations are working hard to answer this question. Some are going passwordless via passkeys. Others, like the Open Researcher and Contributor ID (ORCID), implemented digital identifiers to associate publications, research, and open source contributions with a particular researcher.
Companies focused on advancing identity tech and self-sovereign identity are embracing Decentralized Identifiers (DIDs) as a solution. DIDs are globally unique, alphanumeric, immutable strings representing who you are across the decentralized web.
Speaking of DIDs -- did you know that Decentralized Identifiers are one of the pillars of Web5?

In this post, we'll explore nine more things you may not have known about Decentralized Identifiers.
1. DIDs are a W3C Standard
In 1994, Tim Berners Lee, the creator of the World Wide Web, founded the World Wide Web Consortium (W3C). The W3C is made up of groups of people focused on setting the best practices and standards for building the web. For example, the W3C develops and maintains standards for HTML, CSS, Web Accessibility, and Web Security. In July 2022, The W3C officially published standards for Decentralized Identifiers. This way, technologists would have blueprint for building and managing digital identities as we make the shift towards controlling your own identity on the internet.
2. DIDs can represent more than just humans
While DIDs represent people across the web, they can also represent organizations such as manufacturers, businesses, or government agencies. Technologists are exploring using DIDs to represent IoT devices like smart hubs, smart thermostats, or autonomous cars, allowing you to maintain control over your data usage! Here's a taboo but realistic use case that might make you blush— DIDs can even represent sex tech devices! 😳
3. It's nearly impossible for someone to steal your DID
A common question people often ask me is, "Can someone steal my DID?" DIDs are alphanumeric strings, so they may give people the impression that DIDs are top-secret passwords or API keys. But that's not the case; you can share your DID with anyone without compromising your safety. It's nearly impossible for someone to steal your DID and pretend to be you because DIDs are all cryptographically signed.
What does 'cryptographically signed' mean?
Cryptographically signed means that each DID has a unique digital fingerprint generated by a fancy, complicated algorithm. Two keys—a public key and a private key—make up the digital fingerprint. Your public key shows other people that the DID legitimately belongs to you, but the private key needs to remain private. The private key is like your master key. Someone can only steal your DID, tamper with your DID, or impersonate you if they have access to your private key. Fortunately, it's not easy to access your private key because it is protected by encryption and multiple layers of security. Some DID methods even support key rotation meaning you can update your cryptographic keys to reduce the risk of compromise.
Store your DID in an authenticated digital wallet
In addition to all these security algorithms that protect your DID from being stolen, users typically store their DIDs in an authenticated digital wallet (similar to how your Apple Wallet or Google Wallet stores your debit card information). Storing your DID in a digital wallet provides an additional layer of security because you often have to use a form of authentication like Face ID or a passcode to access items stored in the wallet.

4. Your DID is more than a string
While your DID is a string, it's part of a larger JSON object called a DID document. In addition to the DID string, the DID document includes metadata like:
- Cryptographic keys to prove ownership
- Rules about how your DID can be used, managed, or modified
Below is an example of a DID document:
{
"@context": [
"https://www.w3.org/ns/did/v1",
"https://w3id.org/security/suites/ed25519-2020/v1"
]
"id": "did:example:123456789abcdefghi",
"verificationMethod": [{
"id": "did:example:123456789abcdefghi#key-1",
"type": "Ed25519VerificationKey2020",
"controller": "did:example:123456789abcdefghi",
"publicKeyMultibase": "zH3C2AVvLMv6gmMNam3uVAjZpfkcJCwDwnZn6z3wXmqPV"
}, ...],
"authentication": [
"#key-1"
]
}
Source: https://www.w3.org/TR/did-core/#example-an-example-of-a-relative-did-url
Learn more about DID documents here.
5. Every DID has a DID method
Let's examine the anatomy of a DID method.
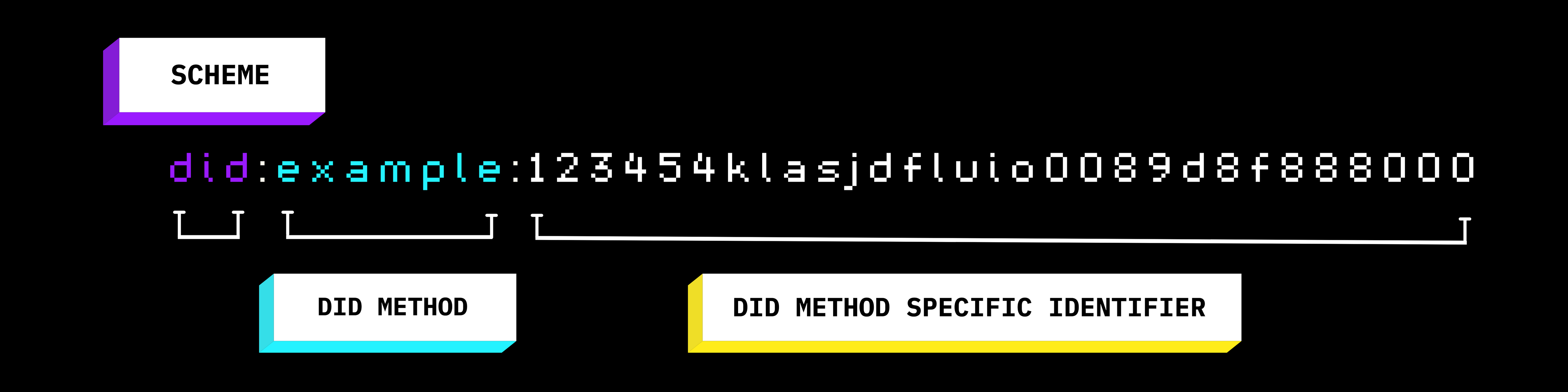
Every DID:
- Starts with the schema
did: - Followed by a word or acronym representing the did method
- Then, ends with a did method-specific identifier in the form of an alphanumeric string
A schema and a DID method together may look like did:web or did:jwk.
What are DID methods?
DID methods define the rules for creating, managing, and deactivating DIDs.
6. There are over 100 DID methods
Anyone can create a DID method. Companies, individuals, or communities may create a custom DID method to fit a specific use case or live on a specific type of ledger. However, to ensure the DID method is recognized, interoperable, and meets the correct standards, it's strongly recommended to include the DID method on the W3C DID Spec Registry.
7. TBD created its own DID method
We (TBD) created our own DID method called DID:DHT. DHT stands for Distributed Hash Table indicating the use of Mainline DHT. You can learn more about DID:DHT via the spec and this blog post written by TBD’s Director of Open Standards, Gabe Cohen.
At TBD, we colloquially call DID:DHT, DID THAT.
8. You don't have to use blockchain; we use BitTorrent
When I hear the words, "decentralized" or "immutable", I immediately think of blockchain and cryptocurrency. I don't think that train of thought is in the minority.
For instance, to ensure DIDs have no central authority and that individual users can own them, folks typically anchor DIDs on an immutable ledger.
What does anchoring a DID mean?
Anchoring a DID means recording DID transactions on a distributed ledger.
DID:DHT uses BitTorrent; not blockchain
At TBD, we actually took a blockchain-less approach. We anchored DID:DHT to BitTorrent. As mentioned above, DID:DHT uses a Mainline DHT, which is a distributed hash table used by the BitTorrent protocol.
9. You can create a DID with the Web5 SDK
You can use the Web5 SDK to create a DID!
Web5.connect()
You can generate a DID using the Web5.connect() method with the following steps:
Install the web5/api package
npm install @web5/api
Import the package
import { Web5 } from '@web5/api';
Call Web5.connect()
const { web5, did: myDid } = await Web5.connect();console.log(myDid)
More ways to create a DID
Check out the documentation to learn more ways to create a DID in various languages including JavaScript, Kotlin, and Swift.
Learn more about Decentralized Identifiers
- Have a question? Ask it in our Discord; we're happy to help!
- Eager to start building? Follow the guides in our documentation.
- Curious about the entire ecosystem? Watch our YouTube videos.